Data Security Guide
Explore the essentials of data security with our in-depth guide. Discover how to safeguard your business in the digital age, understand key regulations, and learn about Segment’s robust security protocols.

Explore the essentials of data security with our in-depth guide. Discover how to safeguard your business in the digital age, understand key regulations, and learn about Segment’s robust security protocols.

Data security is the process of protecting digital information. It includes maintaining its confidentiality, integrity, and restricting its availability to authorized users. Secure data is safeguarded from breaches, theft, corruption, or deletion throughout its entire lifecycle so that it retains value and can’t be used in dangerous ways.
At Segment, we take the responsibility of helping you manage your customer data seriously. That’s why security and privacy are key focus areas for our organization and product development.
It’s becoming increasingly more difficult to protect large volumes of data against risks today –over six million data records were compromised in the first quarter of 2023 across the globe. And according to our annual State of Personalization report, only 51% of consumers trust brands to keep their personal data secure and use it responsibly.
Data has grown to be a top asset among organizations; almost every part of the customer and business life cycle is powered by data, driving deeper insight, improving workflow efficiencies, and helping to grow profitability over time.
But unlike more traditional investments that can be stored in a safe or set up in a trust, data is dynamic, continually growing and changing. New data gets created every millisecond and needs a safe and secure onramp to an organization’s larger data infrastructure.
Companies that incorporate data security measures into every aspect of their business have a better chance of avoiding the new wave of risks happening each year. Data breaches are treacherous because one incident can wipe out the security and safety of so many people at once. Companies that disregard data integrity risk disappointing (and possibly endangering) millions of people, while undermining their credibility as an organization, and potentially facing legal repercussions.
One of the top obstacles to battling data risks is that they constantly change. Currently, the top ways data gets leaked or compromised include:
Accidental leaks: This occurs when someone inadvertently shares, saves, or accesses data that they shouldn’t. While not nefarious, it can be very damaging.
Phishing attacks: This risk most often appears as an email or text that looks like a message from a trusted brand or organization. When the unsuspecting reader opens it, they may be prompted to supply private information later used to steal from or defraud them.
Lack of access controls: It’s essential that only those who need access to data can see it, and even fewer people should be able to save, delete, or adapt it. Without proper access controls for individual users, data is shared wider than it should be and can invite additional risk.
These are just a few of the ways data gets compromised, but they are increasingly difficult to manage with multiple access points. Every tool you use has an additional login and a chance for a breach to occur. This risk gets multiplied for every user in your organization that uses that tool. Add in the increased threat of having dispersed teams possibly working in un-secure settings, and it can be very difficult to keep data where it needs to be at all times.
Data security is such a vital part of running a business, and to ignore it risks putting your customers and their assets in danger.
Segment helps organizations of all sizes safeguard their data, stay compliant with global privacy regulations, and avoid data losses with a platform that’s been designed to deliver 99.9999% uptime (meaning our APIs are always available to accept new data). Let’s take a closer look at these different security features below.
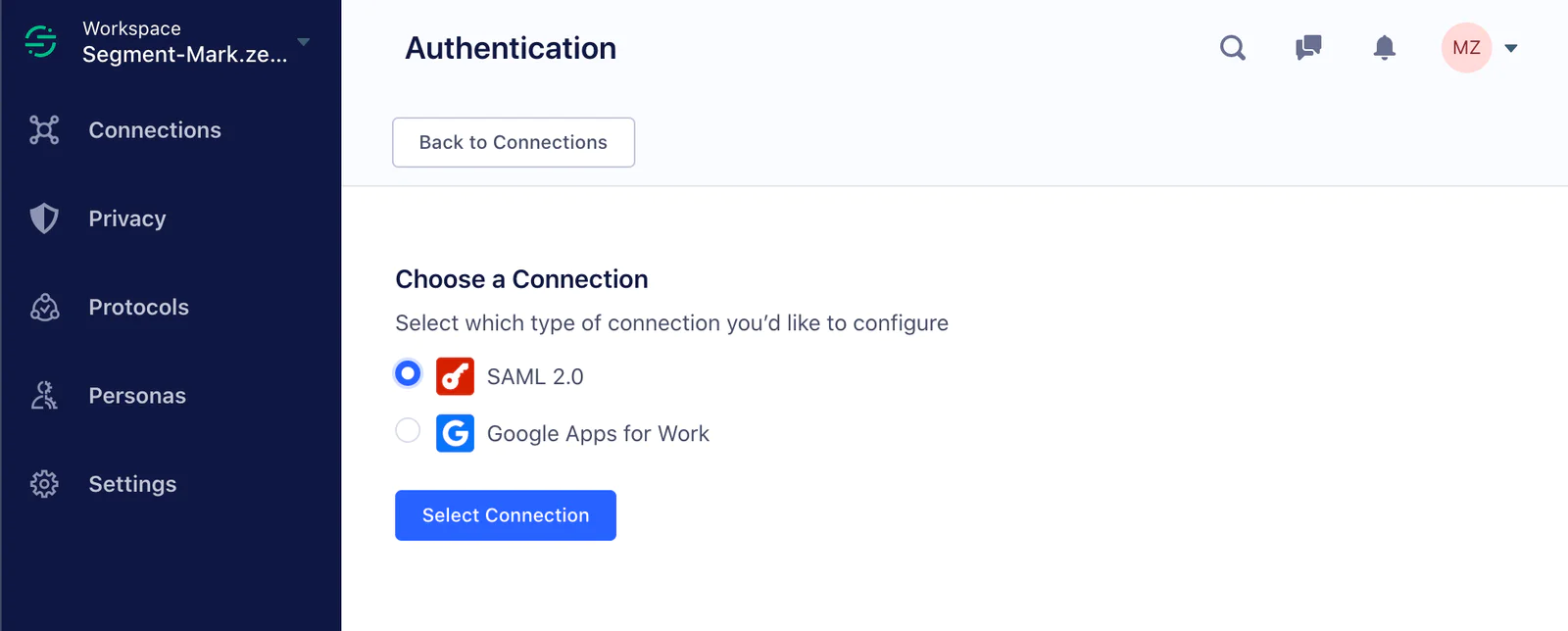
Business users get access to a centrally managed control center through Single Sign-On (SSO), so granting access to Sources and Workspaces to only those you specify is simple. You’ll even get password guidance to discourage reusing passwords that may have been involved in security breaches on other sites or that are too easy to guess.
A layer of login protection, multi-factor authentication (MFA), further bolsters your data security by requiring a confirmation code sent to your mobile device.
Segment’s creation of a bug bounty program in 2017 has fortified security for all customers. It’s run on the Bugcrowd platform and rewards those who discover vulnerabilities with cash for their efforts. Not only has this investment encouraged a proactive approach to finding security issues, but it also harnesses the talent of the tech community to make Segment even better.
Segment has made its technology work within the framework of several industry standards and has certifications to demonstrate this alignment. The company’s commitment to security can be found in its ISO/IEC 27001 compliance and other practices.
Segment does not own or sell its customers’ user data and abides by the GDPR, CCPA, and Privacy Shield Framework requirements. In fact, we believe it’s essential that organizations should own their own analytics data. Segment helps customers access their data in real time via webhooks, S3, and warehouse integrations.
Data security is the action taken to protect data from risks, such as theft, unauthorized access, or loss. Without it, businesses can’t ensure their own data or their customer’s personal information is safe. Not only will a lack of adequate data security put data in harm’s way, but it can leave an organization open to legal penalties, fines, or lawsuits from customers.
Since cybersecurity risks evolve so quickly, staying on top of them requires diligence and a proactive approach. Companies should:
Stay informed through research, educational opportunities, and industry events
Seek the guidance of a professional to help develop, maintain, and adapt data systems
Watch to see what risks are already doing harm and adapt internal practices to thwart danger
Test systems and practice debugging
Data security threats include phishing attacks through employee emails, poor management of access controls, accidental leaks, insider hacking, and employee breaches. Security threats can happen both inside the company and from outside attacks, such as Distributed Denial of Service (DDOS) incidents.
Segment takes many steps to ensure data security, including adhering to data privacy regulations, offering enhanced access controls, using only certified technology, and running a bug bounty program to proactively target vulnerabilities.